
By Solution (Network Security, Data Security, Endpoint Security, Security Orchestration Automation & Response (SOAR), API Security, Security Analytics, Security Policy Management),...... By Authentication Type (Single-factor Authentication, Multi-factor Authentication), By Deployment (Cloud, On-Premise, Hybrid), By Enterprise Size (Small & Medium Enterprises(SMEs), Large Enterprise), By End User (BFSI, IT & Telecom, Retail, Healthcare, Others {Transportation, Manufacturing Industry, Publishing, etc.}), By Country (UAE, Saudi Arabia, Qatar, Israel, Egypt, Kuwait, Others), By Competitors (Palo Alto Networks, Cisco, Illumio, Zscaler, IBM, Akamai, CyberKnight Technologies, Orange, Citrix, Check Point Software Technologies Ltd.) Read more
- ICT & Electronics
- Sep 2024
- 157
- PDF, Excel, PPT
Market Definition
Zero trust security is a cybersecurity framework based on “Never Trust, Always Verify”. Under this, the cybersecurity solution implemented in the organization will constantly need to verify whenever anyone tries to access the data and resources across the micro-segmented network infrastructure irrespective of whether the user or device that generated the access request is present inside or outside the organization's perimeters.
Market Insights & Analysis: Middle East Zero Trust Security Market (2024-30):
The Middle East Zero Trust Security Market size is valued at USD2.41 billion in 2024 & is projected to reach USD7.4 billion by 2030. Along with this, the market is estimated to grow at a CAGR of around 17.14% during the forecast period, i.e., 2024-30. The increasing number of cyber threats from within and outside the organizations in the Middle East has led to the growing demand for zero-trust security solutions in the region. The zero trust security based on the idea “never trust always verify” has made it a standard when implementing cybersecurity solutions. The increasing digitalization of Middle Eastern countries due to the implementation of technologies such as cloud computing, the Internet of Things, machine learning, blockchain, artificial intelligence, and data analytics are being implemented by organizations and governments in the region.
| Report Coverage | Details |
|---|---|
| Historical Years | 2019-22 |
|
Base Years
|
2023
|
|
Forecast Years
|
2024-30
|
| Market Value in 2024 | USD 2.41 Billion |
| Market Value (2030) | USD 7.4 Billion |
| CAGR (2024-30) | 17.14% |
| Leading Region | UAE |
| Top Key Players | Check Point Software Technologies, Cloudflare, Sophos, CyberArk, IBM, Microsoft, CyberKnight Technologies, Orange, Citrix, Palo Alto Networks, Fortinet, and Others |
| Key Report Highlights |
|
*Boost strategic growth with in-depth market analysis - Get a free sample preview today!
The transition toward creating a digital economy is part of the overall strategy of the region to gradually shift towards the non-oil sectors. For instance, it is estimated that artificial intelligence will alone have an economic impact of more than USD 300 billion on the Middle Eastern geography. Additionally, increasing adoption of the cloud in the region as nearly 70% of the companies in the region are planning to migrate to a cloud-based system by 2025. This along with the boom in the e-commerce and Fintech industry will further widen the digital landscape of the Middle East. The expanding digital landscape would expose a lot more vulnerabilities that will be exploited by cyber adversaries to launch more cyber-attacks. Such developments will further boost the demand for the zero trust security solution in the Middle East.
Middle East Zero Trust Security Market Driver:
Rising Cyber Threats in the Region– The critical requirement to develop cybersecurity capabilities to guard against escalating threats from cyber adversaries is the primary driver of the zero-trust security market in the Middle East. The region is experiencing massive cyber-attacks related to data breaches. In 2024, the Middle East has average data breach cost has risen by 8.4% to USD 8.75 million per incident on a YoY basis according to IBM. Moreover, the average data breach cost per incident is substantially higher compared to the global average data breach cost of USD 4.88 million. These data breaches greatly disrupt business activities in the Middle East. Furthermore, they also drive up business costs by increasing the expenses associated with regulatory compliances and activities post-cyber breach.
- Market Segmentation
- Introduction
- Product Definition
- Research Process
- Assumption
- Executive Summary
- Middle East IT Security Investment 2019-2030F
- Middle East Zero Trust Security Market Policies and Regulations
- Middle East Zero Trust Security Market Dynamics
- Drivers
- Challenges
- Impact Analysis
- Middle East Zero Trust Security Market Trends & Insights
- Middle East Zero Trust Security Market Business Cases, By End Users
- BFSI
- IT & Telecom
- Retail
- Healthcare
- Others
- Middle East Zero Trust Security Market Hotspots & Opportunities
- Middle East Security Zero Trust Security Market Outlook, 2019-2030F
- Market Size & Analysis
- By Revenues (USD Billion)
- Market Share & Analysis
- By Component
- By Solution
- Network Security- Market Size & Forecast 2019-2030, USD Million
- Data Security- Market Size & Forecast 2019-2030, USD Million
- Endpoint Security- Market Size & Forecast 2019-2030, USD Million
- Security Orchestration Automation & Response (SOAR)- Market Size & Forecast 2019-2030, USD Million
- API Security- Market Size & Forecast 2019-2030, USD Million
- Security Analytics- Market Size & Forecast 2019-2030, USD Million
- Security Policy Management- Market Size & Forecast 2019-2030, USD Million
- By Services
- Consulting and Advisory Services
- Implementation and Integration Services
- Managed Services
- Training and Support Services
- By Solution
- By Authentication Type
- Single Sign-On (SSO)- Market Size & Forecast 2019-2030, USD Million
- Multi-factor Authentication (MFA)- Market Size & Forecast 2019-2030, USD Million
- By Deployment
- Cloud- Market Size & Forecast 2019-2030, USD Million
- On-Premise- Market Size & Forecast 2019-2030, USD Million
- Hybrid- Market Size & Forecast 2019-2030, USD Million
- By Enterprise Size
- Small & Medium Enterprises(SMEs)- Market Size & Forecast 2019-2030, USD Million
- Large Enterprise- Market Size & Forecast 2019-2030, USD Million
- By End User
- BFSI- Market Size & Forecast 2019-2030, USD Million
- IT & Telecom- Market Size & Forecast 2019-2030, USD Million
- Retail- Market Size & Forecast 2019-2030, USD Million
- Healthcare- Market Size & Forecast 2019-2030, USD Million
- Others (Transportation, Manufacturing Industry, Publishing, etc.)
- By Country
- UAE
- Saudi Arabia
- Qatar
- Israel
- Egypt
- Kuwait
- Others
- By Company
- Competition Characteristics
- Revenue Shares
- By Component
- Market Size & Analysis
- UAE Zero Trust Security Market Outlook, 2019-2030F
- Market Size & Analysis
- By Revenue (USD Million/Billion)
- Market Share & Analysis
- By Solution- Market Size & Forecast 2019-2030, USD Million
- By Authentication Type- Market Size & Forecast 2019-2030, USD Million
- By Deployment- Market Size & Forecast 2019-2030, USD Million
- By Enterprise Size- Market Size & Forecast 2019-2030, USD Million
- By End User- Market Size & Forecast 2019-2030, USD Million
- Market Size & Analysis
- Saudi Arabia Zero Trust Security Market Outlook, 2019-2030F
- Market Size & Analysis
- By Revenue (USD Million/Billion)
- Market Share & Analysis
- By Solution- Market Size & Forecast 2019-2030, USD Million
- By Authentication Type- Market Size & Forecast 2019-2030, USD Million
- By Deployment- Market Size & Forecast 2019-2030, USD Million
- By Enterprise Size- Market Size & Forecast 2019-2030, USD Million
- By End User- Market Size & Forecast 2019-2030, USD Million
- Market Size & Analysis
- Qatar Zero Trust Security Market Outlook, 2019-2030F
- Market Size & Analysis
- By Revenue (USD Million/Billion)
- Market Share & Analysis
- By Solution- Market Size & Forecast 2019-2030, USD Million
- By Authentication Type- Market Size & Forecast 2019-2030, USD Million
- By Deployment- Market Size & Forecast 2019-2030, USD Million
- By Enterprise Size- Market Size & Forecast 2019-2030, USD Million
- By End User- Market Size & Forecast 2019-2030, USD Million
- Market Size & Analysis
- Israel Zero Trust Security Market Outlook, 2019-2030F
- Market Size & Analysis
- By Revenue (USD Million/Billion)
- Market Share & Analysis
- By Solution- Market Size & Forecast 2019-2030, USD Million
- By Authentication Type- Market Size & Forecast 2019-2030, USD Million
- By Deployment- Market Size & Forecast 2019-2030, USD Million
- By Enterprise Size- Market Size & Forecast 2019-2030, USD Million
- By End User- Market Size & Forecast 2019-2030, USD Million
- Market Size & Analysis
- Egypt Zero Trust Security Market Outlook, 2019-2030F
- Market Size & Analysis
- By Revenue (USD Million/Billion)
- Market Share & Analysis
- By Solution- Market Size & Forecast 2019-2030, USD Million
- By Authentication Type- Market Size & Forecast 2019-2030, USD Million
- By Deployment- Market Size & Forecast 2019-2030, USD Million
- By Enterprise Size- Market Size & Forecast 2019-2030, USD Million
- By End User- Market Size & Forecast 2019-2030, USD Million
- Market Size & Analysis
- Kuwait Zero Trust Security Market Outlook, 2019-2030F
- Market Size & Analysis
- By Revenue (USD Million/Billion)
- Market Share & Analysis
- By Solution- Market Size & Forecast 2019-2030, USD Million
- By Authentication Type- Market Size & Forecast 2019-2030, USD Million
- By Deployment- Market Size & Forecast 2019-2030, USD Million
- By Enterprise Size- Market Size & Forecast 2019-2030, USD Million
- By End User- Market Size & Forecast 2019-2030, USD Million
- Market Size & Analysis
- Competitive Benchmarking
- Companies Profile (Business Description, Products Diversification, Solutions, Assets, Target Market, Partnership, Merger & Acquisition, etc.)
- Check Point Software Technologies
- Product Portfolio
- Target Markets
- Target Security Type
- Research & Development
- Strategic Alliances
- Strategic Initiatives
- Cloudflare
- Product Portfolio
- Target Markets
- Target Security Type
- Research & Development
- Strategic Alliances
- Strategic Initiatives
- Sophos
- Product Portfolio
- Target Markets
- Target Security Type
- Research & Development
- Strategic Alliances
- Strategic Initiatives
- CyberArk
- Product Portfolio
- Target Markets
- Target Security Type
- Research & Development
- Strategic Alliances
- Strategic Initiatives
- IBM
- Product Portfolio
- Target Markets
- Target Security Type
- Research & Development
- Strategic Alliances
- Strategic Initiatives
- Microsoft
- Product Portfolio
- Target Markets
- Target Security Type
- Research & Development
- Strategic Alliances
- Strategic Initiatives
- CyberKnight Technologies
- Product Portfolio
- Target Markets
- Target Security Type
- Research & Development
- Strategic Alliances
- Strategic Initiatives
- Orange
- Product Portfolio
- Target Markets
- Target Security Type
- Research & Development
- Strategic Alliances
- Strategic Initiatives
- Citrix
- Product Portfolio
- Target Markets
- Target Security Type
- Research & Development
- Strategic Alliances
- Strategic Initiatives
- Palo Alto Networks
- Product Portfolio
- Target Markets
- Target Security Type
- Research & Development
- Strategic Alliances
- Strategic Initiatives
- Fortinet
- Product Portfolio
- Target Markets
- Target Security Type
- Research & Development
- Strategic Alliances
- Strategic Initiatives
- Others
- Check Point Software Technologies
- Companies Profile (Business Description, Products Diversification, Solutions, Assets, Target Market, Partnership, Merger & Acquisition, etc.)
- Disclaimer

MarkNtel Advisors follows a robust and iterative research methodology designed to ensure maximum accuracy and minimize deviation in market estimates and forecasts. Our approach combines both bottom-up and top-down techniques to effectively segment and quantify various aspects of the market. A consistent feature across all our research reports is data triangulation, which examines the market from three distinct perspectives to validate findings. Key components of our research process include:
1. Scope & Research Design At the outset, MarkNtel Advisors define the research objectives and formulate pertinent questions. This phase involves determining the type of research—qualitative or quantitative—and designing a methodology that outlines data collection methods, target demographics, and analytical tools. They also establish timelines and budgets to ensure the research aligns with client goals.
2. Sample Selection and Data Collection In this stage, the firm identifies the target audience and determines the appropriate sample size to ensure representativeness. They employ various sampling methods, such as random or stratified sampling, based on the research objectives. Data collection is carried out using tools like surveys, interviews, and observations, ensuring the gathered data is reliable and relevant.
3. Data Analysis and Validation Once data is collected, MarkNtel Advisors undertake a rigorous analysis process. This includes cleaning the data to remove inconsistencies, employing statistical software for quantitative analysis, and thematic analysis for qualitative data. Validation steps are taken to ensure the accuracy and reliability of the findings, minimizing biases and errors.
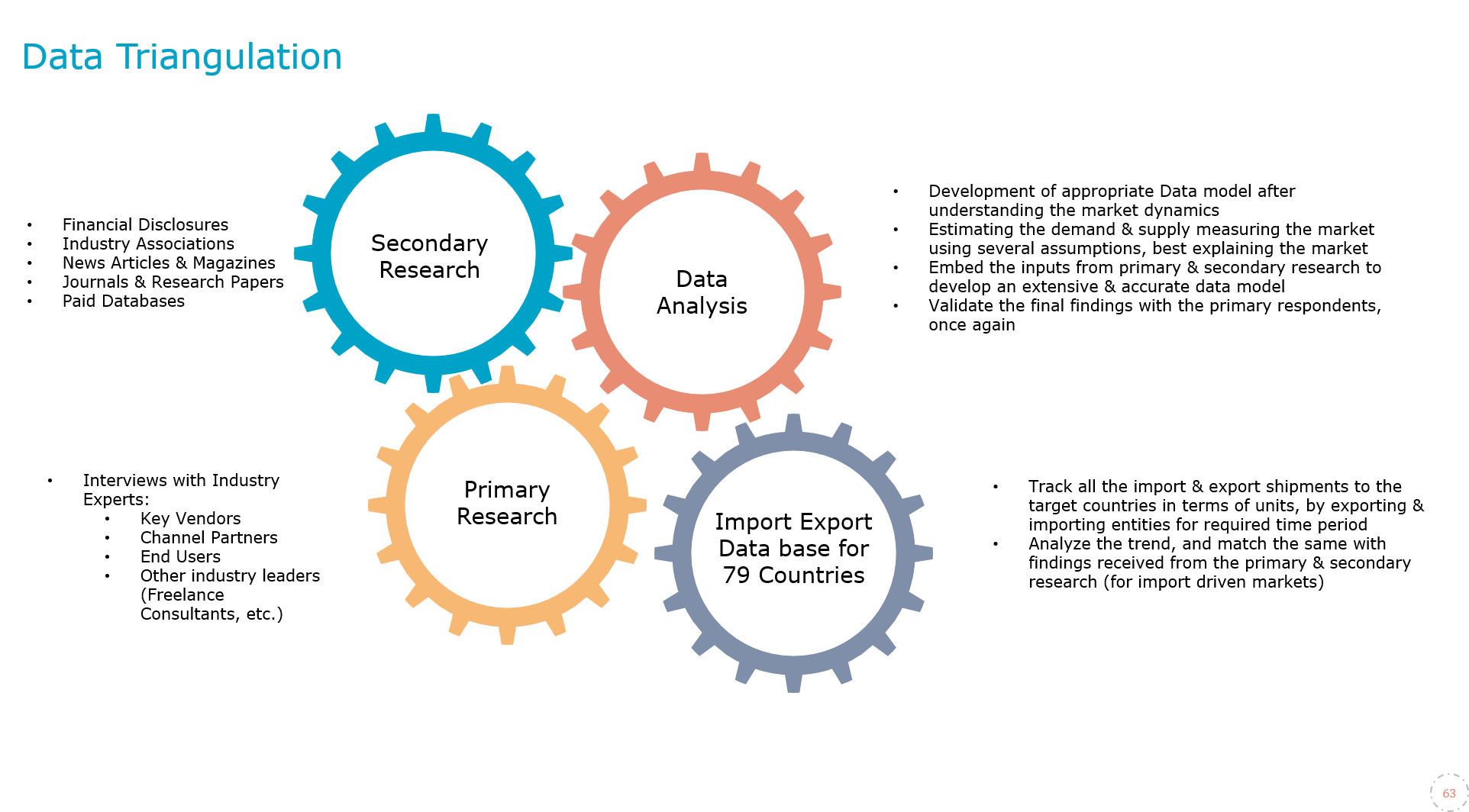
4. Data Forecast and FinalizationThe final phase involves forecasting future market trends based on the analyzed data. MarkNtel Advisors utilize predictive modeling and time series analysis to anticipate market behaviors. The insights are then compiled into comprehensive reports, featuring visual aids like charts and graphs, and include strategic recommendations to inform client decision-making
FILL THE FORM TO GET THE FREE SAMPLE PAGES
